Which Statement Best Describes a Unified Threat Management Device
Domain 4b - Medium Question 1 0 2 points Implementation of Unified Threat Management is a popular security strategy that uses a single dedicated device to implement a broad range of network security functions. Characteristics of unified threat management UTM include all of the following except.
Which option describes the best defense against collusion.

. It combines security performance management and compliance capabilities into a single installation making it easier for. Which device is able to stop activity that is considered to be suspicious based on. The advantages of combining everything into one include a reduced learning curve you only have one product to learn a.
Which statement best describes a Unified threat management device. UTM fully integrates all of the security functions installed on the device. Which scenario would best warrant the implementation of a RADIUS server.
An IDS is a passive monitoring device that detects potential threats and. A firewall takes an active effort to block unauthorized access to the network. Managed centrally and therefore reduces.
Routers operate at which layer of the OSI model. When you combine a firewall with other abilities intrusion prevention antivirus content filtering etc what used to be called an all-in-one appliance is now known as a unified threat management UTM system. If the UTM crashes that will cause a single point of.
Which VPN technology is currently considered the preferred method for securely connecting a remote endpoint device back to an enterprise network. Which of the following issues can cause UTM to be a less than satisfactory solution. An all-inclusive business communications solution that is a part of Fortinet Security Fabric.
It is important to carefully consider the deployment scenario. This brings us to software based modules in Unified Threat Management UTM devices. A firewall acts as a gateway for the network and can actively block unauthorized access based on.
A multiplexing method based on coded signlas. An all-in-one security device. An all-in-one security device.
Intrusion prevention system. A unified threat management solution which integrates multiple technologies in one system can provide more comprehensive. Firewalls establish barriers between secured and controlled internal networks that can be trusted and untrusted outside networks such as the internet.
Unified threat management UTM describes an information security infosec system that provides a single point of protection against threats including viruses worms spyware and other malware and network attacks. Firewalls can be hardware software or. Short for Unified Threat Management a UTM is a networking device or software program that helps reduce the complexity of securing a network.
Usually a UTM is used in a corporate environment. Obviously they can only be located where the UTM itself is located. Which statement describes a VoIP Gateway.
To enable secure access to web applications on a corporate intranet or extranet an SSL a VPN concentrator can be installed alongside all of the following except which option. During a penetration test you find a file containing hashed passwords for the system you are attempting to breach. Key items to point out about these devices happen to be drawbacks though this does not reduce their efficacy.
A cloud-based solution in Unified Communications. Affordable and requires no capital expenses. A proxy server acts as a relay to establish a connection to an external point.
It is the means of translating between the VoIP network and external voice networks. It accomplishes this by including an anti-malware content filter firewall intrusion detection and spam protection into a single package. Which security control can best protect against shadow IT by identifying and preventing use of unsanctioned cloud apps and services.
Which statement best describes CDMA. A firewall is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules. Which device could be classified as a next generation firewall.
Unified threat management gateway. In some cases an IDS may be the best choice for the job while in others the. Which statement best describes a Unified Threat Management device.
The term Unified Threat Management UTM refers to a network security solution commonly in the form of a dedicated device called a UTM appliance or a web security gateway which combines the functionality of a firewall with additional safeguards such as URL filtering content inspection spam filtering gateway antivirus protection IDSIPS functionality or malware. The advantages of combining everything into one include a reduced learning curve you only have. Identify the statement that correctly describes FortiVoice.
Both a proxy server and a firewall act as a gateway for network traffic. Software based modules in UTM devices. When you combine a firewall with other abilities intrusion prevention antivirus content filtering etc what used to be called an all-in-one appliance is now known as a unified threat management UTM system.

Network Firewall An Overview Sciencedirect Topics
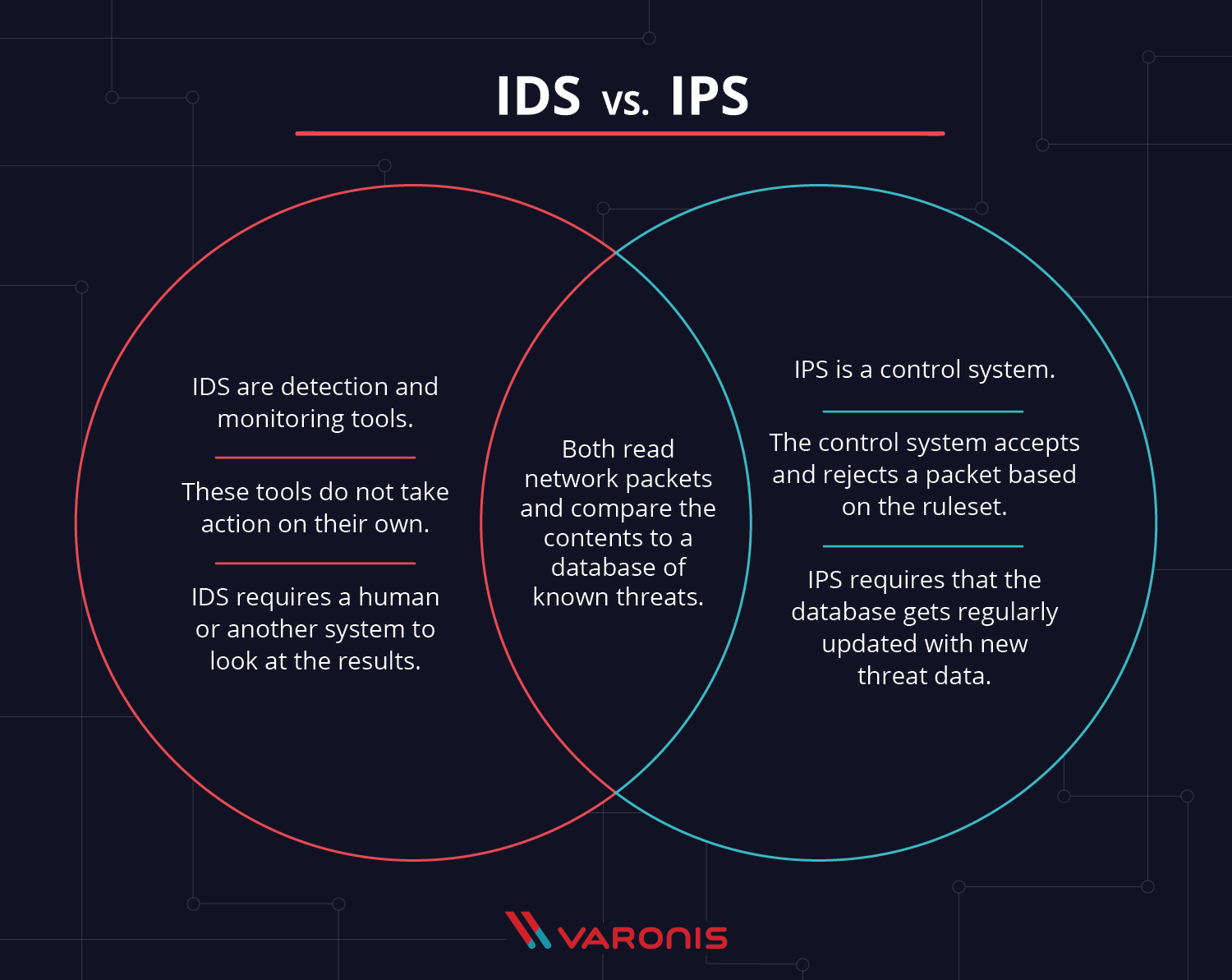
Ids Vs Ips What Is The Difference

Network Firewall An Overview Sciencedirect Topics
Mis Ch08 Securing Information Systems

Small Business It Solutions In 2021 Supportive Support Services Small Business
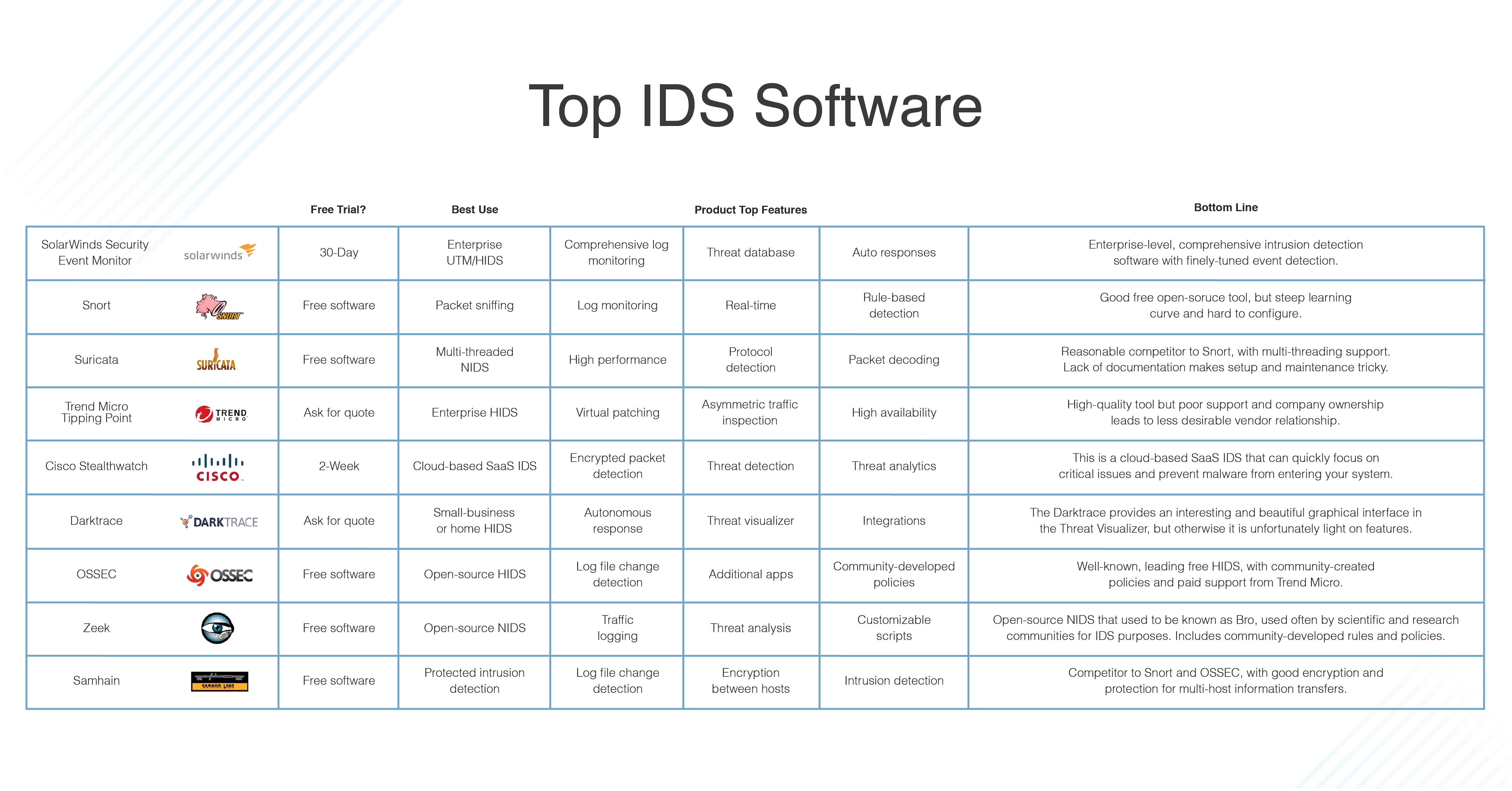
What Is An Intrusion Detection System Definition Types And Tools Dnsstuff

The Five Phases Of The Threat Intelligence Lifecycle Flashpoint

Sangfor Endpoint Secure Sangfor
Pdf A Unified Classification Model Of Insider Threats To Information Security

Threat Management Incident Response Compuquip

How To Choose A Firewall For Your Business Updated

Threat Management Incident Response Compuquip

What Are The Types Of Network Devices

What Is A Cyber Threat Definition Types Hunting Best Practices And Examples Toolbox It Security

Performance Optimization Strategies For Network Functions Virtualization Lenovo Press

Sangfor Endpoint Secure Sangfor

Network Security Devices You Need To Know About

The Five Phases Of The Threat Intelligence Lifecycle Flashpoint

Comments
Post a Comment